Is the Russian Embassy in Helsinki tracking your phone? Probably they can’t do it (from there)
The Russian Embassy located in Helsinki has gained some attention due to its several antennae positioned at the roofs of the embassy buildings. Ilta-Sanomat has even published claims by a CEO (Aapo Cederberg) of a security consulting company Cyberwatch, that it is possible that Russia has the ability to monitor mobile phone usage, and their locations at the Helsinki city center.
Firstly, I find this kind of serious claim really vague and therefore dangerous to the general public to cause unnecessary panic amongst them, and secondly, there are much better ways to achieve this kind of surveillance goal if some kind of entity has those.
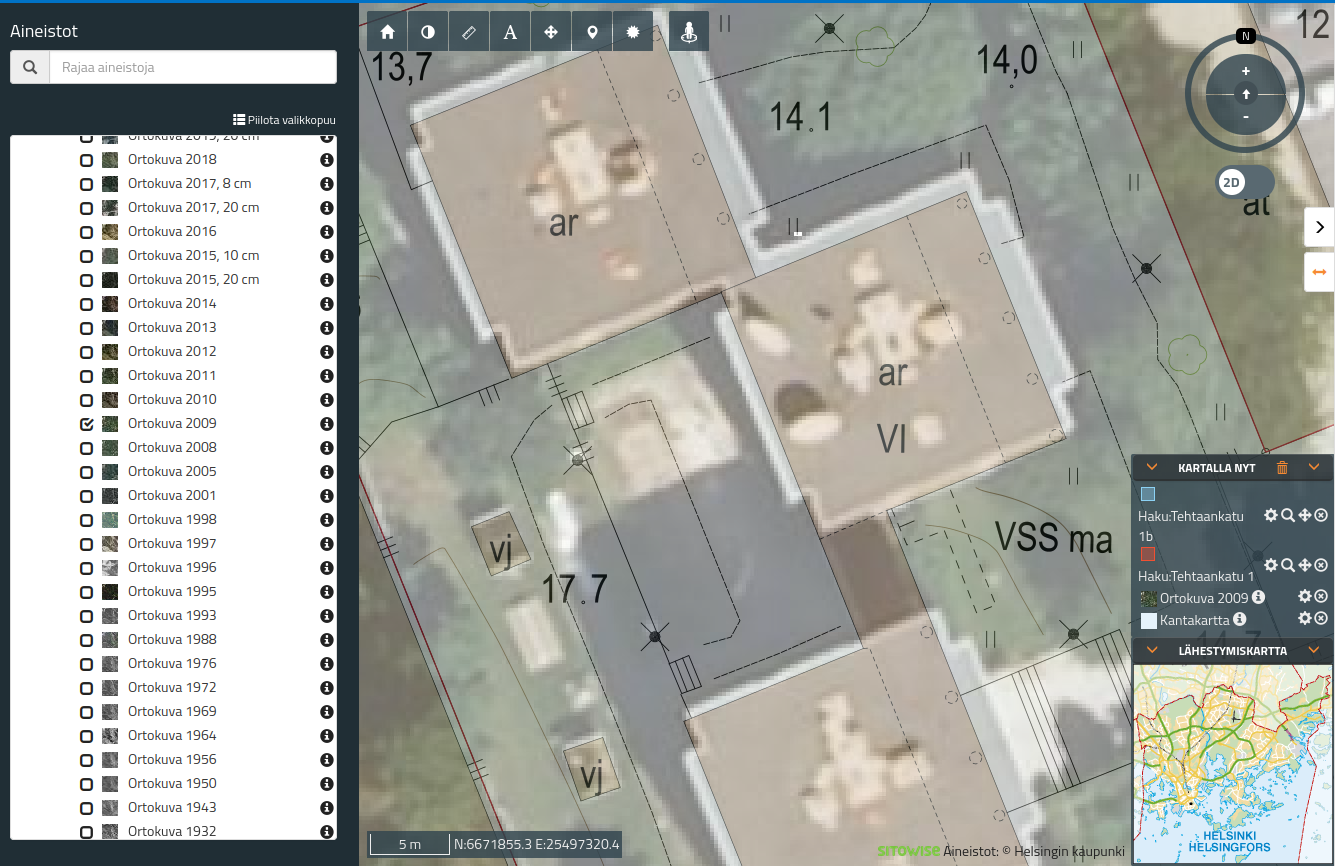
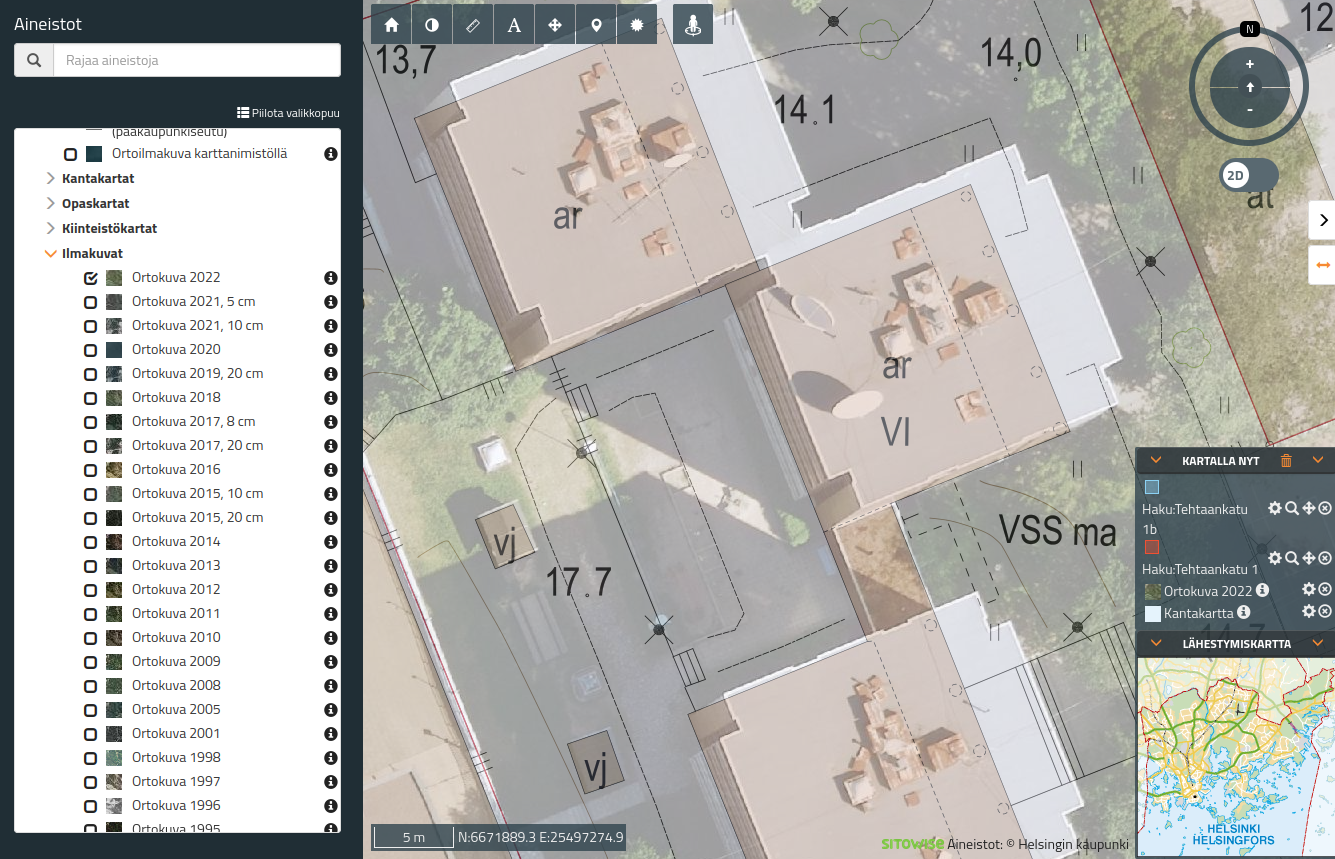
The existence of the antennae is evident from aerial photographs of the embassy. There are 3 larger parabolic (dish) antennae on the roof, however, the direction of these is more like pointed toward the sky instead of possible land-based targets, so their purpose for surveillance isn’t remarkable. The more likely use case of these is probably to keep the embassy connected with their home country in case other connection means can’t be used and/or trusted.
Taking even the mobile phone base station cell size used in the city into account, I would say if the embassy wanted to listen to mobile phone communications they could only do it very nearby their embassy. The cell sizes in the city tend to be small and they’re low-powered due to the demand for mobile connectivity limiting the surveillance range to tens to a few hundred meters.
Finally, it should be noted that these antennae have been in the same positions for years (The City of Helsinki map service). The pictures below are from 2009, 2015, and 2022 respectively. It would be quite surprising that the Finnish intelligence services or foreign intelligence services hadn’t monitored these antennae before and taken proper countermeasures:
 |
 |
 |
|---|---|---|
| 2009 | 2015 | 2022 |
How about the better/other ways for tracking?
For location tracking there is a famous way, the mobile phone signaling system no. 7 or SS7 as parts of standards and protocols from the 1970s when things like SMS were implemented. Due to its age, there are several vulnerabilities in the protocol that have been discovered and despite its age, the SS7 is still in use.
Any party with access to the SS7 network can use the network’s trust-based design to determine a cell phone location by triangulating its location in most cases. Triangulation happens from knowing to which mobile cells a mobile phone is connected to and the used signal strength. The SS7 then has a feature to request this information with its ‘Any Time Interrogation’ function. The required information for the query is the mobile phone number of the target.
For things that are more likely oriented for usage tracking, there are IMSI catchers and related vectors that are dependent on the target network type. However, as stated in that article too, the active methods require really close proximity to the targets and the smallest false base stations can have the size of a suitcase.